I’ve known about DD-WRT for a while and always wanted to play with it (partly because I thought it was needed to do this prank of turning the Internet upside down). My router is leased from Time Warner and probably not supported by DD-WRT. So I bought an Asus RT-N16 router and learned how to flash DD-WRT firmware onto it. The process was easier than I expected but required me to read a lot and be careful. I sifted through mazes of documentation, blog posts, and forum threads to find the most recent and correct ones. I was afraid of bricking my brand new $100 Asus, but I succeeded. Here’s how you can too.
What is DD-WRT and why would you install it?
DD-WRT is open-source Linux-based firmware that can replace and enhance the factory default firmware on many wireless routers. Once you install it, you can SSH, overclock the CPU, setup advanced access restrictions, change the firewall, etc.
How to install DD-WRT onto an Asus RT-N16 wireless router
Follow this guide written specifically for the Asus RT-N16 and flash the initial firmware dd-wrt.v24-14929_NEWD-2_K2.6_mini_RT-N16.trx here in step 3. Then in step 7, flash the dd-wrt.v24-18024_NEWD-2_K2.6_mega build to get most of the features.
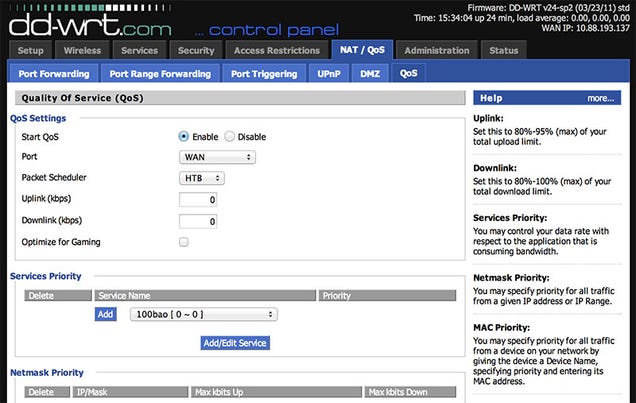
Read everything carefully and make sure to follow all the steps. If you open your router’s web UI and see the below, give yourself a pat on the back.
Setup SSH access to router
Go to the web UI. Click on the “Services” tab and scroll down to the “Secure Shell” section. Enable SSHd and add your SSH public key.

Now you can ssh root@<router's IP>.
Mount a USB hard drive for network-attached storage
I quickly discovered, thanks to my colleague Andrey, that the Asus has a read-only file system. The only way to write anything to it is to mount an external hard disk. Luckily USB disks are cheap, this can act as a file server/network-attached storage, and it’s easy to do.
I bought a ~$25 64GB Sandisk USB. The first step is to format and partition it (I used a Linux machine). I didn’t create the “jffs” partition because I had a USB instead of a multimedia card or “MMC”.

Plug the USB into the Asus router and follow these steps here. You’ll know you’ve mounted the
USB correctly when you can touch /opt/test if /opt was your mount point.
Install extra software using ipkg
For someone who’s used to advanced shells like fish and zsh, I was sad to see I was
always root (is there a way to create more user accounts?) running sh. There’s vi but no vim,
no --help or man pages for commands, and not even error messages (you have to echo $?). So I
followed these steps to install ipkg, the Itsy Package Management System, into /opt.
I didn’t bother creating /opt/etc/profile. I just use ipkg-opt instead of the built-in ipkg,
and things seem to work. I installed the following packages:
1 2 3 4 5 6 | |
As I’m writing this, I see that ipkg has been discontinued and that opkg supersedes it. I haven’t tried out opkg yet.
The background behind the limited functionality of DD-WRT’s operating system is that it’s built on top of BusyBox, a single executable providing a very stripped-down version of Linux. BusyBox was specifically created for embedded operating systems.
Known bugs in DD-WRT v24-sp2 mega revision 18024
- the router’s SSH keys change everytime it reboots
- NAT loopback doesn’t work. I worked around it with the iptables rules below.
1 2 3 4 | |
This is explained here where the writer claims allowing NAT loopback doesn’t make your internal network less secure. I think the reason for the disabled NAT loopback is to prevent DNS rebinding attacks. This DefCon talk by Craig Heffner explains it nicely.
There’s an option to enable “No DNS rebind” in DD-WRT though. Maybe that prevents this vulnerability?